AI models have moved from assisting developers to performing serious security research workflows. Anthropic's Claude Mythos Preview is one of the clearest examples of that shift. In its April 2026 technical write-up, Anthropic describes a model that can autonomously discover and sometimes exploit complex vulnerabilities across operating systems, browsers, and critical open source software.
That matters for one reason: cybersecurity has always been a race between attacker speed and defender speed. If model-assisted research accelerates both sides, companies that update slowly, triage slowly, and patch slowly will be exposed faster than before.
In this guide, we break down what Mythos Preview is, why Anthropic launched Project Glasswing instead of a public release, what the benchmark and field results suggest, where developers can access the model, and what practical actions security teams should take right now.
What Is Claude Mythos Preview?
Claude Mythos Preview is Anthropic's newest frontier model announced with Project Glasswing. Anthropic frames it as a general-purpose model with unusually strong performance on code, reasoning, and autonomous security tasks.
Key positioning points:
- It is not a broadly public model release.
- It is being rolled out in a controlled partner program.
- It is designed to help defenders secure critical systems before similar capabilities become widely available.
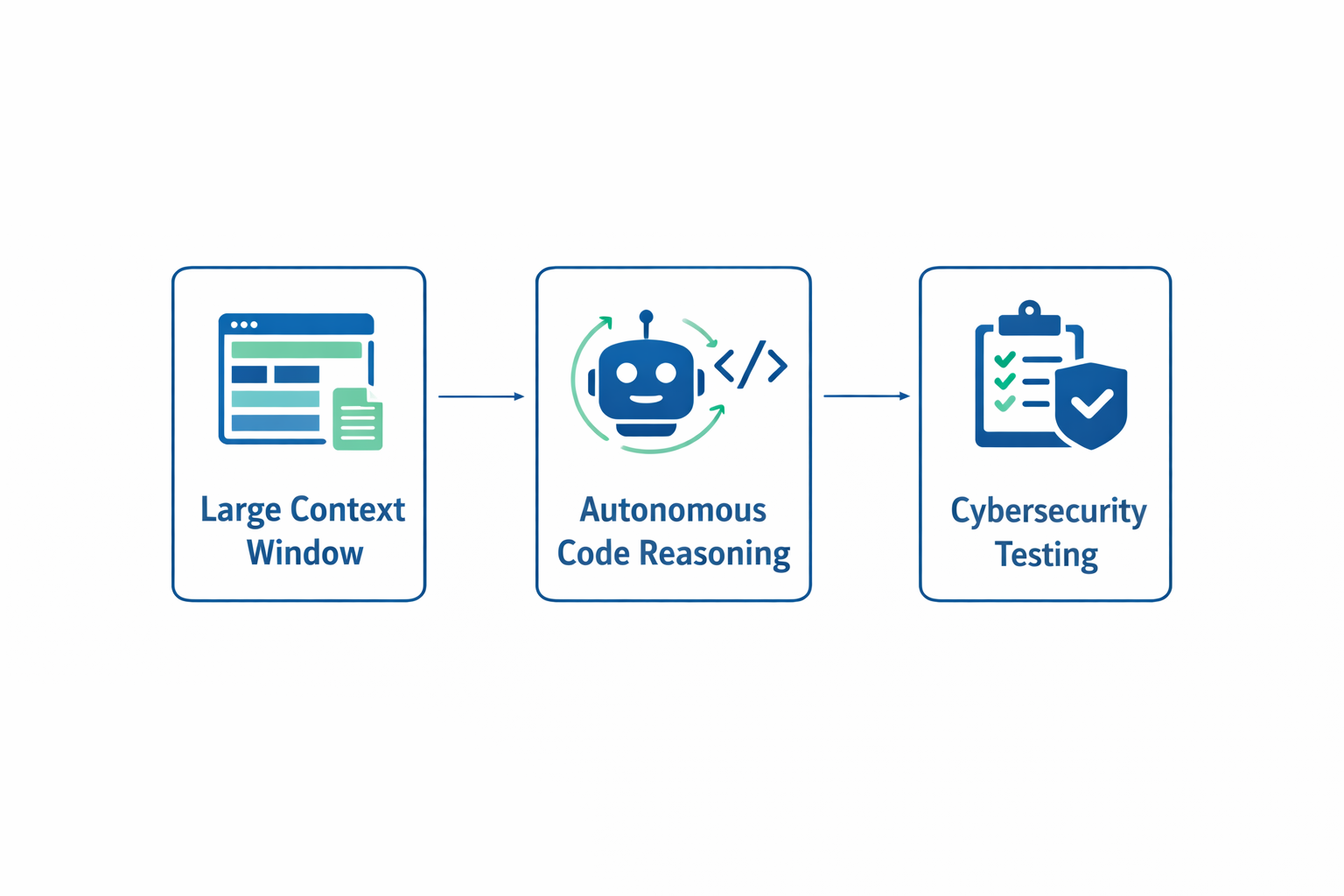
Anthropic also states that Mythos Preview can work with very large contexts, including up to 1M tokens in supported environments, which makes it suitable for large codebase analysis and multi-step agentic workflows.
Why This Announcement Is a Big Cybersecurity Signal
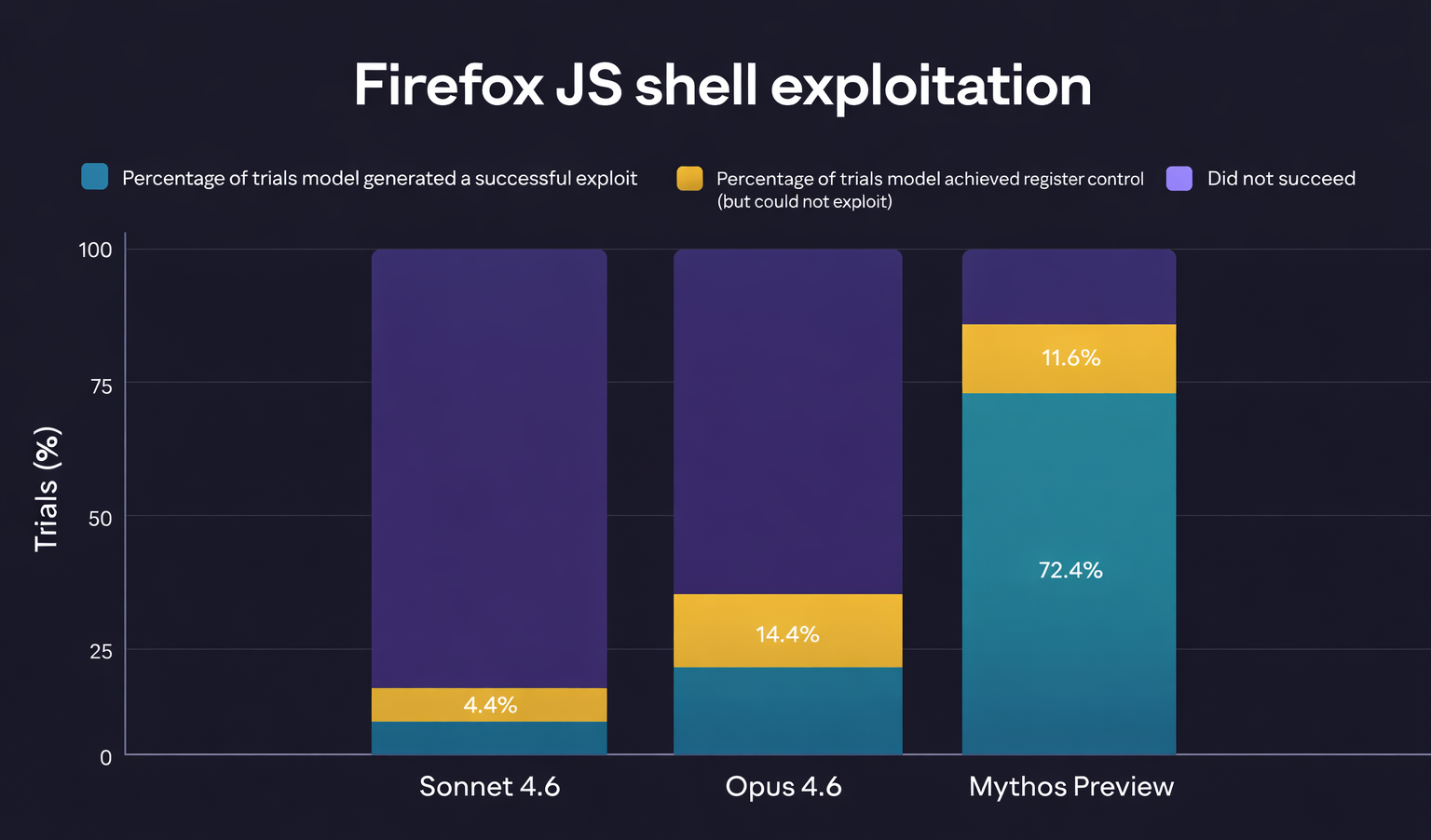
Most prior model updates improved vulnerability detection. Mythos Preview appears to improve both vulnerability discovery and exploit construction in a way Anthropic describes as a step change.
In Anthropic's own testing narrative, Mythos Preview:
- Found deep, old, and subtle vulnerabilities.
- Chained multiple weaknesses to produce higher-impact outcomes in some environments.
- Performed autonomous multi-step workflows with less human intervention than earlier model generations.
This does not mean every output is instantly production-ready, and it does not remove the need for human validation. But it does suggest that both red-team and blue-team work can scale faster than traditional manual processes.
How Anthropic Evaluated Mythos Preview
Anthropic's technical post describes a repeatable agentic scaffold rather than a one-off demo. Their process generally involves:
- Running isolated environments for target software.
- Prompting the model to find vulnerabilities.
- Letting it inspect code, run tests, refine hypotheses, and generate reports.
- Running additional validation and triage before disclosure.
They also describe coordinated disclosure constraints, including staged validation and delayed publication of technical details while patches are in progress. That approach is important because premature detail releases can increase exploitation risk.
Benchmark and Field Highlights
Based on Anthropic's public materials and the broader Mythos reference summary, several claims stand out:
- Very high software engineering benchmark performance (including strong SWE-bench outcomes).
- Significant improvement over earlier Anthropic models in exploit-oriented tasks.
- Demonstrated ability to uncover vulnerabilities in mature codebases that have seen years of review.
It is important to read these as directional capability signals, not as a guarantee that every run yields a critical finding. Real-world vulnerability work still depends on target quality, orchestration, environment setup, and human review discipline.
Project Glasswing and the Limited Access Model
Anthropic did not launch Mythos Preview as a general API tier for everyone. Instead, it introduced Project Glasswing with a restricted partner model.
Why this matters:
- Anthropic is signaling that capability growth is outpacing existing safeguards.
- The company is treating deployment as a security governance problem, not only a product launch.
- The transition period is seen as high risk, especially if offensive automation improves faster than defensive adoption.
In practice, this means Mythos Preview access is currently tied to selected organizations and controlled usage pathways, rather than open self-serve onboarding.
Where and How Developers Can Use It
For approved users, Mythos Preview follows familiar cloud model integration patterns. Anthropic and partner ecosystem references indicate usage through:
- Anthropic API surfaces.
- Amazon Bedrock.
- Google Vertex AI.
- Microsoft-associated partner routes for enterprise deployment.
From a developer experience perspective, this is useful: teams can often keep similar integration architecture (prompts, orchestration, tool-calling, logging), while swapping model IDs and adjusting governance controls.
Pricing, Cost Reality, and Operational Planning
Mythos Preview has been described as a premium capability tier with notably higher token pricing than standard production models. Whether you are in the access cohort now or preparing for similar models later, cost planning matters.
For security teams, the correct question is not just "cost per token." It is:
- Cost per validated critical finding.
- Cost per fixed vulnerability.
- Cost per day reduced in triage and patch windows.
A model can be expensive but still provide strong ROI if it reduces severe incident exposure and shortens remediation cycles.
Risks, Criticism, and Open Questions
A balanced view is important. Alongside impressive results, there are valid concerns:
- Some published examples are easier to verify than others due to disclosure limits.
- Not every discovered issue has equal severity or practical exploitability.
- Public claims may be interpreted as both security warning and competitive positioning.
- Independent, large-scale third-party replication is still limited.
These caveats do not invalidate the broader trend. They simply reinforce that organizations should make decisions using measured threat modeling, not hype.
What Security Teams Should Do Right Now
Even without Mythos access, most teams can take immediate defensive steps.
- Tighten patch SLAs for internet-facing systems and critical dependencies.
- Increase automated vulnerability triage capacity to avoid backlog growth.
- Expand secure code review with model-assisted workflows in CI.
- Rehearse coordinated disclosure and emergency patch communication playbooks.
- Prioritize hardening that creates true barriers, not just friction.
If model-driven exploit construction keeps improving, the biggest competitive advantage for defenders will be operational speed.
Timeline Snapshot
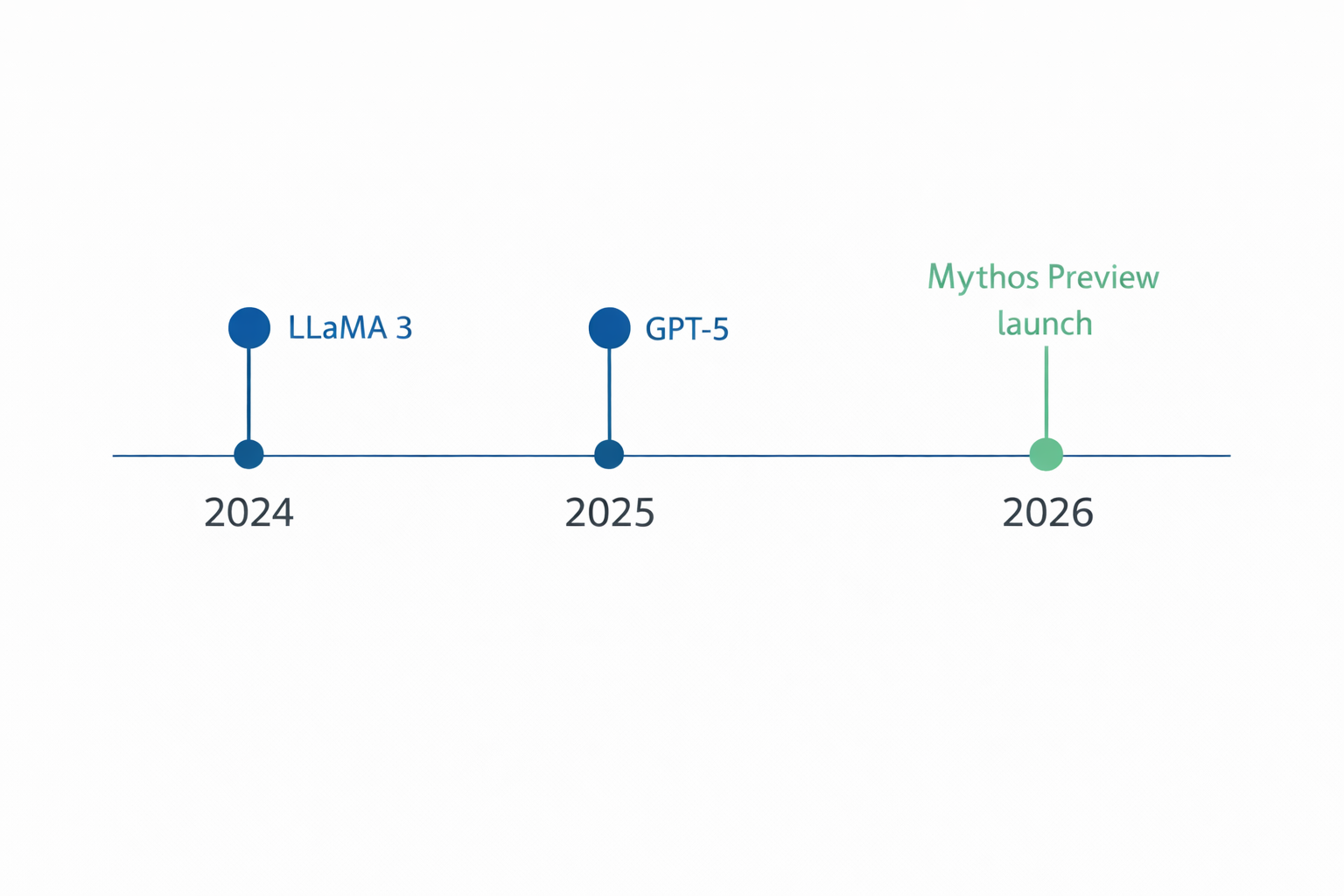
A simple timeline helps place this announcement in context:
- March 2026: Broader industry discussion and leaks around Mythos-class capability claims.
- April 7, 2026: Anthropic publishes the Mythos Preview cybersecurity technical post and launches Project Glasswing.
- Following months: Controlled partner testing, responsible disclosure cycles, and safeguard development for future deployment.
Final Takeaway
Mythos Preview should be treated as a cybersecurity inflection point, not just another model release. The core message is clear: model capability is accelerating, and the security operating model must accelerate with it.
For engineering leaders, the practical move is to modernize defensive workflows now: faster triage, faster patching, stronger validation, and AI-augmented secure development practices. Teams that wait for perfect clarity may lose valuable response time.
If your organization wants to design an AI-assisted secure development pipeline, Duo Dev Technologies can help you implement practical workflows for vulnerability review, remediation prioritization, and secure release operations.
Sources
- Anthropic Frontier Red Team: Assessing Claude Mythos Preview's cybersecurity capabilities
- Anthropic Project Glasswing announcement